TITLE I – GENERAL PROVISIONS (Articles 1-2)
Article 1 – Subject matter and scope
Article 1 defines the subject matter and scope of the Regulation by establishing: (i) the mission, objectives, tasks and organisational framework of ENISA; (ii) a Union framework for European cybersecurity certification schemes applicable to ICT products, services, processes, managed security services and the cybersecurity posture of entities; and (iii) a trusted ICT supply chain framework addressing non-technical cybersecurity risks. It clarifies that the Regulation aims to ensure a high level of cybersecurity, enhance trust in the digital environment, and support the functioning of the internal market.
Article 2 – Definitions
Article 2 provides detailed definitions applicable throughout the Regulation, including terms relating to cybersecurity risks, incidents and threats, crisis management structures, national and Union actors such as CSIRTs and competent authorities, as well as certification-related concepts such as European cybersecurity certification schemes, certificates, EU statements of conformity, assurance levels, conformity assessment bodies, accreditation, technical specifications and cybersecurity skills attestation schemes.
TITLE II – THE EUROPEAN UNION AGENCY FOR CYBERSECURITY (Articles 3-70)
Chapter I – Mission and Objectives (Articles 3-4)
Article 3 – Mission of ENISA
Article 3 establishes ENISA’s mission as supporting Member States and Union institutions, bodies, offices and agencies in achieving a high level of cybersecurity, contributing to trust in the digital environment, facilitating cooperation across the Union, and acting as a reference point for expertise, advice, guidance and information on cybersecurity matters.
Article 4 – Objectives of ENISA
Article 4 sets out ENISA’s objectives, including supporting the implementation of Union cybersecurity policy and law, enhancing preparedness and operational cooperation, contributing to cybersecurity certification and standardisation, supporting the development of cybersecurity skills and workforce, improving awareness, and facilitating cooperation with stakeholders, including at international level.
Chapter II – Tasks (Articles 5-23)
Section 1 – Support for implementation of Union policy and law (Articles 5-9)
Article 5 – Support for implementation of Union cybersecurity law
Article 5 assigns ENISA the task of supporting the consistent implementation of Union cybersecurity law by Member States and Union entities, including through the development of guidelines, recommendations, methodologies, technical assistance, best practices, and facilitation of information exchange and coordination across sectors and authorities.
Article 6 – Capacity-building and strategic support
Article 6 entrusts ENISA with strengthening cybersecurity capacities at national and Union level, including activities related to prevention, detection, analysis and response to cyber threats and incidents, support for the establishment, development and functioning of CSIRTs, and contributions to the preparation, implementation and review of national and Union cybersecurity strategies and policies.
Article 7 – Awareness and outreach activities
Article 7 requires ENISA to carry out awareness-raising and outreach activities, including organising campaigns, producing guidance material, supporting training initiatives, and promoting good practices aimed at improving cybersecurity awareness among citizens, businesses and public authorities.
Article 8 – Market analysis and monitoring
Article 8 mandates ENISA to monitor, analyse and report on developments in the cybersecurity market, including trends in supply and demand, emerging technologies, vulnerabilities and threats, and to provide relevant technical and market intelligence to Member States, Union institutions and stakeholders.
Article 9 – International cooperation
Article 9 provides for ENISA’s role in international cooperation, including participation in international fora, cooperation with third countries and international organisations, exchange of information and best practices, and support to the Union’s external cybersecurity policies and initiatives.
Section 2 – Operational coordination (Articles 10-16)
Article 10 – Operational cooperation and coordination mechanisms
Article 10 establishes ENISA’s role in facilitating operational cooperation at Union level among Member States, Union institutions, bodies, offices and agencies, and relevant stakeholders. It provides for ENISA to support secure information exchange, coordination of actions in response to cross-border cybersecurity incidents and the development of mechanisms enabling cooperation and coordination between competent authorities, including those designated under Union cybersecurity legislation.
Article 11 – Development and support of cyber threat intelligence
Article 11 tasks ENISA with developing and supporting cyber threat intelligence capabilities at Union level. It provides for the collection, aggregation, analysis and dissemination of information relating to cyber threats, vulnerabilities and incidents, including the development of methodologies, tools and platforms supporting threat intelligence sharing and the enhancement of situational awareness among Member States and Union entities.
Article 12 – Early warning, alerting and information dissemination
Article 12 provides for ENISA’s role in issuing early warnings and alerts relating to cybersecurity threats and incidents. It establishes that ENISA shall identify emerging risks, disseminate timely and relevant information to competent authorities and stakeholders, and support coordinated preventive and response actions, including through structured communication channels.
Article 13 – EU Cybersecurity Reserve and crisis support
Article 13 entrusts ENISA with the operation and coordination of the EU Cybersecurity Reserve. It provides for the mobilisation of resources and expertise to support preparedness, response and recovery in the event of significant or large-scale cybersecurity incidents. It also establishes ENISA’s role in coordinating assistance to affected entities and Member States, including in situations involving major disruptions such as ransomware attacks.
Article 14 – Cybersecurity exercises and preparedness activities
Article 14 requires ENISA to support and coordinate cybersecurity exercises at Union level. It provides for the compilation of a programme of exercises, facilitation of participation by Member States and relevant stakeholders, and the organisation of exercises upon request. It also establishes the role of ENISA in evaluating exercises, identifying lessons learned and supporting improvements in preparedness and response capabilities.
Article 15 – Tools, platforms and incident reporting support
Article 15 assigns ENISA responsibility for developing, operating and maintaining tools and platforms supporting operational coordination. It includes systems for harmonised incident reporting, secure communication channels, coordination platforms and integration with Union-level reporting mechanisms, ensuring interoperability and facilitating the exchange of information between competent authorities and stakeholders.
Article 16 – Vulnerability management and coordination services
Article 16 establishes ENISA’s role in developing and supporting Union-level vulnerability management capabilities and services. It provides for activities related to the identification, analysis and coordination of vulnerabilities, including support for coordinated vulnerability disclosure processes, facilitation of information sharing between relevant actors and contribution to remediation efforts across Member States.
Section 3 – Cybersecurity certification and standardisation (Articles 17-18)
Article 17 – Certification schemes support
Article 17 establishes ENISA’s role in the development, implementation and maintenance of European cybersecurity certification schemes, including preparing candidate schemes upon request, supporting their consistent application, providing guidance, and contributing to capacity-building related to certification across Member States.
Article 18 – Standardisation activities
Article 18 requires ENISA to contribute to European and international standardisation activities, including participation in standard-setting organisations, development of technical specifications, coordination with stakeholders, and ensuring alignment between certification schemes and applicable standards.
Section 4 – Cybersecurity Skills Academy (Articles 19-23)
Article 19 – European Cybersecurity Skills Framework
Article 19 defines ENISA’s role in supporting the European Cybersecurity Skills Framework, including contributing to its development, maintenance, promotion and alignment with Union policies on education, training and workforce development.
Article 20 – Skills attestation schemes
Article 20 entrusts ENISA with developing and maintaining voluntary European cybersecurity skills attestation schemes for individuals, including defining criteria, procedures, assessment methods and conditions for issuing attestations.
Article 21 – Authorisation of attestation providers
Article 21 sets out requirements for the authorisation of attestation providers, including competence, independence, organisational capacity, compliance with applicable rules, and ongoing monitoring of authorised providers.
Article 22 – Application procedures for authorisation
Article 22 establishes procedures for the submission and assessment of applications for authorisation, including documentation requirements, evaluation criteria, timelines for decisions, and conditions for granting, suspending or withdrawing authorisation.
Article 23 – Transparency of attestation schemes
Article 23 requires ENISA to publish information on attestation schemes, authorised providers, procedures and requirements, ensuring transparency, accessibility and recognition of cybersecurity skills across the Union.
Table 1. Tasks of ENISA under the Cybersecurity Act
| Article | Title / Chapter / Section | Task area | Description of tasks |
| Article 5 | Title II – Chapter II – Section 1 | Support for implementation of Union law | ENISA supports the consistent implementation of Union cybersecurity law by Member States and Union entities, including through guidance, methodologies, best practices, technical assistance and facilitation of information exchange. |
| Article 6 | Title II – Chapter II – Section 1 | Capacity-building and strategic support | ENISA contributes to strengthening cybersecurity capacities at national and Union level, including prevention, detection and analysis of cyber threats and incidents, support to CSIRTs, and contribution to cybersecurity strategies. |
| Article 7 | Title II – Chapter II – Section 1 | Awareness and outreach | ENISA carries out awareness-raising and outreach activities, including campaigns, guidance, training support and promotion of good practices. |
| Article 8 | Title II – Chapter II – Section 1 | Market analysis | ENISA monitors and analyses the cybersecurity market, including supply and demand, emerging technologies, vulnerabilities and threats, and provides technical and market intelligence. |
| Article 9 | Title II – Chapter II – Section 1 | International cooperation | ENISA contributes to international cooperation, including participation in international fora, cooperation with third countries and organisations, and exchange of information and best practices. |
| Article 10 | Title II – Chapter II – Section 2 | Operational cooperation | ENISA supports operational cooperation at Union level, including secure information exchange and coordination in response to cross-border incidents. |
| Article 11 | Title II – Chapter II – Section 2 | Cyber threat intelligence | ENISA develops and supports cyber threat intelligence capabilities, including collection, analysis and dissemination of information. |
| Article 12 | Title II – Chapter II – Section 2 | Early warning and alerts | ENISA identifies emerging threats and issues early warnings and alerts to competent authorities and stakeholders. |
| Article 13 | Title II – Chapter II – Section 2 | EU Cybersecurity Reserve | ENISA operates and coordinates the EU Cybersecurity Reserve, supporting preparedness, response and recovery. |
| Article 14 | Title II – Chapter II – Section 2 | Cybersecurity exercises | ENISA supports and coordinates cybersecurity exercises, including organisation and evaluation. |
| Article 15 | Title II – Chapter II – Section 2 | Tools and platforms | ENISA develops and operates tools and platforms, including systems for incident reporting and coordination. |
| Article 16 | Title II – Chapter II – Section 2 | Vulnerability management | ENISA supports vulnerability management, including identification, analysis and coordinated disclosure. |
| Article 17 | Title II – Chapter II – Section 3 | Certification schemes | ENISA develops, implements and maintains European cybersecurity certification schemes. |
| Article 18 | Title II – Chapter II – Section 3 | Standardisation | ENISA contributes to standardisation activities and development of technical specifications. |
| Article 19 | Title II – Chapter II – Section 4 | Cybersecurity skills framework | ENISA supports the European Cybersecurity Skills Framework. |
| Article 20 | Title II – Chapter II – Section 4 | Skills attestation schemes | ENISA develops and maintains voluntary cybersecurity skills attestation schemes. |
| Article 21 | Title II – Chapter II – Section 4 | Authorisation of providers | ENISA establishes requirements for authorisation of attestation providers. |
| Article 22 | Title II – Chapter II – Section 4 | Application procedures | ENISA manages application procedures for authorisation of providers. |
| Article 23 | Title II – Chapter II – Section 4 | Transparency of schemes | ENISA publishes information on attestation schemes and providers. |
| Article 75 | Title III – Chapter I | Maintenance of certification schemes | ENISA coordinates maintenance of certification schemes, including updates and stakeholder involvement. |
| Article 76 | Title III – Chapter I | Evaluation of schemes | ENISA evaluates certification schemes periodically. |
| Article 77 | Title III – Chapter I | Technical specifications | ENISA develops and publishes technical specifications supporting certification schemes. |
| Article 79 | Title III – Chapter I | Public information platform | ENISA maintains a public platform on certification schemes and certificates. |
Chapter III – Organisation of ENISA (Articles 24-44)
Section 1 – Management Board
Article 24 – Structure and governance bodies
Article 24 sets out ENISA’s administrative and governance structure by establishing its constituent bodies, including the Management Board, the Executive Board, the Executive Director, the Deputy Executive Director, the ENISA Advisory Group and the Board of Appeal, and defining their respective roles within the Agency’s institutional framework.
Article 25 – Composition of the Management Board
Article 25 establishes the composition of the Management Board, providing for one representative per Member State and two representatives appointed by the Commission, and ensuring balanced participation in the Agency’s strategic governance.
Article 26 – Chairperson and Deputy Chairperson
Article 26 sets out the procedures for the selection of the Chairperson and Deputy Chairperson of the Management Board, including eligibility, voting arrangements and duration of mandates.
Article 27 – Meetings and functioning of the Management Board
Article 27 governs the organisation, frequency and conduct of Management Board meetings, including rules on convening meetings, participation and decision-making procedures.
Article 28 – Functions and responsibilities of the Management Board
Article 28 defines the functions of the Management Board, including the adoption of the Agency’s programming document, budgetary oversight, supervision of the Executive Director and general strategic direction of ENISA.
Article 29 – Voting arrangements of the Management Board
Article 29 establishes the voting rules applicable within the Management Board, including quorum requirements and majority thresholds for decision-making.
Section 2 Executive Board
Article 30 – Executive Board
Article 30 establishes the Executive Board as a supporting body to the Management Board, defining its role in assisting with the preparation of decisions, monitoring implementation and overseeing administrative and budgetary matters.
Section 3 Executive Director
Article 31 – Appointment and term of the Executive Director
Article 31 sets out the procedures for the appointment, term of office, extension and dismissal of the Executive Director, including the roles of the Commission and the Management Board.
Article 32 – Tasks and powers of the Executive Director
Article 32 defines the responsibilities of the Executive Director, including managing ENISA, implementing its work programme, ensuring budget execution and representing the Agency legally.
Section 4 Deputy Executive Director
Article 33 – Establishment of the Deputy Executive Director
Article 33 provides for the creation of the position of Deputy Executive Director to support the Executive Director in carrying out management tasks.
Article 34 – Responsibilities of the Deputy Executive Director
Article 34 sets out the functions of the Deputy Executive Director, including assisting or replacing the Executive Director where necessary.
Section 5 – ENISA Advisory Group
Article 35 – ENISA Advisory Group
Article 35 establishes the ENISA Advisory Group as a consultative body supporting the Agency’s activities. It defines its role as providing advice and expertise to ENISA on the execution of its tasks and on strategic and technical cybersecurity matters falling within its mandate. The Article provides that the Advisory Group is composed of representatives of relevant stakeholders, including industry, small and medium-sized enterprises, academic and research organisations, and other experts, ensuring a broad and balanced representation of the cybersecurity ecosystem. It sets out that the Advisory Group contributes to ENISA’s work by offering input on priorities, work programmes, and specific activities, including certification, operational cooperation and capacity-building. It further provides for the organisation and functioning of the Advisory Group, including rules on appointment, participation and procedures, as well as transparency and the management of potential conflicts of interest.
Section 6 – Board of Appeal
Article 36 – Establishment of the Board of Appeal
Article 36 establishes the Board of Appeal as an independent body within ENISA.
Article 37 – Composition and independence of the Board of Appeal
Article 37 defines the composition, appointment and independence requirements of the Board of Appeal.
Article 38 – Conflicts of interest and recusal rules
Article 38 sets out rules on conflicts of interest and recusal for members of the Board of Appeal.
Article 39 – Scope of appealable acts
Article 39 defines which decisions or failures to act by ENISA may be subject to appeal.
Article 40 – Right and procedure to appeal
Article 40 establishes the conditions under which natural and legal persons may lodge appeals, including procedural requirements and deadlines.
Article 41 – Interlocutory revision procedure
Article 41 provides for the possibility of ENISA revising its decision before the appeal is examined by the Board of Appeal.
Article 42 – Examination and decisions on appeals
Article 42 governs the procedure for examining appeals and the adoption of decisions by the Board of Appeal.
Article 43 – Judicial review before the Court of Justice
Article 43 provides for the possibility of bringing actions before the Court of Justice of the European Union following the exhaustion of internal appeal procedures.
Section 7 – Operations
Article 44 – Programming document and planning
Article 44 establishes ENISA’s single programming document as the central planning instrument governing the Agency’s activities. It provides that the document shall cover both annual and multiannual programming, including the definition of objectives, priorities, expected results and the allocation of human and financial resources. The Article sets out the procedures for the preparation of the programming document by the Executive Director, its adoption by the Management Board, and its submission to the Commission, the European Parliament and the Council. It further establishes requirements for updating the document where necessary, as well as monitoring and reporting on its implementation, including performance indicators and evaluation of results achieved. It also provides for consistency between the programming document and the Union’s broader policy objectives and financial framework.
Chapter IV – Budget (Articles 45-55)
Article 45 – Budget preparation and adoption
Article 45 sets out the procedure for preparing and adopting ENISA’s budget, including the roles of the Executive Director, Management Board and Commission.
Article 46 – Budget structure and resources
Article 46 defines the structure of the budget, including sources of revenue and categories of expenditure.
Article 47 – Fees for certification and attestation activities
Article 47 establishes the framework for levying fees related to certification schemes, attestation schemes and related activities, including cost-recovery principles.
Article 48 – Budget implementation
Article 48 assigns responsibility for implementing the budget to the Executive Director.
Article 49 – Accounts and discharge procedure
Article 49 governs the preparation, presentation and discharge of ENISA’s accounts.
Article 50 – Financial rules
Article 50 provides for the adoption of financial rules applicable to ENISA.
Article 51 – Anti-fraud and audit provisions
Article 51 establishes provisions to prevent fraud and allows for audits and investigations by Union bodies.
Article 52 – Declarations of interests and independence
Article 52 requires declarations of interests from relevant actors to ensure independence and avoid conflicts.
Article 53 – Transparency and access to information
Article 53 requires ENISA to ensure access to objective and reliable information.
Article 54 – Confidentiality obligations
Article 54 governs the protection of confidential information.
Article 55 – Access to documents regime
Article 55 establishes rules on access to ENISA documents in accordance with Union law.
Chapter V – Staff and liaison officers (Articles 56-59)
Article 56 – Staff regime and security clearance
Article 56 establishes that ENISA staff are subject to Union staff regulations and security clearance requirements.
Article 57 – Privileges and immunities framework
Article 57 applies Union privileges and immunities to ENISA and its staff.
Article 58 – Designation and role of liaison officers
Article 58 requires Member States and the Commission to designate liaison officers and defines their functions in facilitating cooperation and information exchange.
Article 59 – Seconded personnel and external experts
Article 59 governs the use of seconded national experts and other non-staff personnel.
Chapter VI – General provisions concerning ENISA (Articles 60-70)
Article 60 – Legal status and capacity
Article 60 establishes ENISA as a Union body with legal personality.
Article 61 – Seat of the Agency
Article 61 confirms the location of ENISA’s seat.
Article 62 – Headquarters agreement
Article 62 requires the conclusion of a headquarters agreement with the host Member State.
Article 63 – Administrative oversight
Article 63 provides for oversight by the European Ombudsman.
Article 64 – Liability and jurisdiction
Article 64 governs ENISA’s liability and the jurisdiction of the Court of Justice.
Article 65 – Language regime
Article 65 establishes rules on language use and translation.
Article 66 – Personal data protection
Article 66 applies Union data protection rules to ENISA.
Article 67 – Security of information
Article 67 requires ENISA to adopt rules for handling classified and sensitive information.
Article 68 – Cooperation with Union bodies and authorities
Article 68 provides for cooperation with Union institutions, agencies and national authorities.
Article 69 – Cooperation with stakeholders
Article 69 establishes the framework for ENISA’s cooperation with stakeholders across the cybersecurity ecosystem. It provides that the Agency shall engage with relevant stakeholders, including industry, small and medium-sized enterprises, conformity assessment bodies, academic and research organisations, and other experts, in order to support the execution of its tasks. The Article specifies that such cooperation may take place through structured interactions, including consultations, exchanges of information, participation in expert groups and other forms of collaboration, including public-private partnerships. It further provides that ENISA may support and facilitate the involvement of stakeholders in activities related to cybersecurity certification, standardisation, capacity-building and operational cooperation. The Article also establishes that cooperation shall ensure transparency, inclusiveness and balanced representation, and shall take into account the need to safeguard confidentiality, security and the proper handling of sensitive information.
Article 70 – Cooperation with third countries and organisations
Article 70 allows cooperation with third countries and international organisations.
TITLE III – EUROPEAN CYBERSECURITY CERTIFICATION FRAMEWORK (Articles 71-97)
Chapter I – Objectives, scope and procedures (Articles 71-79)
Article 71 – Establishment and scope of the certification framework
Article 71 establishes the European cybersecurity certification framework, defining its scope as covering ICT products, services, processes, managed security services and the cybersecurity posture of entities, and providing for the issuance of European cybersecurity certificates and EU statements of conformity that are recognised across all Member States, while maintaining the voluntary nature of certification unless otherwise required under Union law.
Article 72 – Transparency and stakeholder participation – European Cybersecurity Certification Assemblies
Article 72 establishes requirements to ensure transparency and stakeholder participation in the development and functioning of the European cybersecurity certification framework. It provides that the Commission, with the support of ENISA, shall organise European Cybersecurity Certification Assemblies on a regular basis, bringing together Member States, industry representatives, conformity assessment bodies, standardisation organisations, and other relevant stakeholders to discuss strategic priorities, ongoing developments and future needs relating to certification schemes. The Article further requires the establishment and maintenance of a dedicated public website containing information on requested, ongoing and adopted certification schemes, including their scope, objectives, development status and relevant documentation. It also provides for the facilitation of structured exchanges between the Commission, ENISA, Member States and stakeholders, including consultations and information-sharing activities, in order to support transparency, coordination and informed participation throughout the lifecycle of certification schemes.
Article 73 – Initiation of certification schemes
Article 73 sets out the procedure for initiating certification schemes, including the possibility for the Commission or the European Cybersecurity Certification Group to request ENISA to develop a candidate scheme, and specifies the elements to be included in such requests, including scope, objectives, development plan and applicable technical specifications.
Article 74 – Development, assessment and adoption of schemes
Article 74 governs the preparation of candidate schemes by ENISA, including consultation with stakeholders and Member States, submission to the Commission, evaluation within defined timelines and adoption by the Commission through implementing acts, including provisions for requesting revisions or discontinuing the process.
Article 75 – Maintenance of certification schemes
Article 75 establishes the framework governing the maintenance of European cybersecurity certification schemes following their adoption. It provides that each scheme shall include a maintenance strategy addressing updates in light of technological developments, changes in standards and evolving cybersecurity risks. The Article assigns ENISA a central role in supporting the maintenance of schemes, including through the organisation of maintenance activities and coordination mechanisms. It further provides for the involvement of the Commission and the European Cybersecurity Certification Group in a consultative capacity, including through the exchange of views, provision of input and support for coordination. The Article also underlines stakeholder involvement, including through consultations and the possible establishment of ad hoc expert working groups, as well as the collection of feedback from certification practice. It further provides for the monitoring of the consistent application of schemes across Member States and the identification of elements requiring updates or adjustments.
Article 76 – Evaluation, review and withdrawal of certification schemes
Article 76 establishes a periodic evaluation mechanism for European cybersecurity certification schemes. It provides that ENISA shall assess each scheme at least every four years, taking into account technological developments, market evolution, stakeholder feedback and the practical implementation of the scheme. The Article further provides that, on the basis of these evaluations and in consultation with ENISA, the European Cybersecurity Certification Group and relevant stakeholders, the Commission may decide to maintain, revise or withdraw a scheme. It specifies that such decisions shall be adopted through implementing acts and may take into account the continued relevance, effectiveness and coherence of the scheme within the Union legal framework.
Article 77 – Development and publication of technical specifications
Article 77 provides that ENISA may develop and maintain technical specifications supporting European cybersecurity certification schemes. It establishes that such technical specifications may be used for both the development of new schemes and the maintenance of existing ones. The Article requires ENISA to publish these technical specifications on its website, ensuring accessibility and transparency, while also providing that certain specifications may not be published where this is justified by security considerations. It further provides that these technical specifications support the implementation of schemes without modifying their scope or legal effects.
Article 78 – Presumption of conformity with Union law
Article 78 provides that European cybersecurity certificates and EU statements of conformity issued under a certification scheme may confer a presumption of conformity with specific requirements set out in Union legal acts. It establishes that such presumption applies where the relevant scheme is referenced in those legal acts and where the applicable requirements are covered by the certification scheme. The Article thereby links certification schemes with compliance mechanisms under Union law, without altering the voluntary nature of certification unless otherwise specified.
Article 79 – Public information and transparency platform
Article 79 requires ENISA to maintain a publicly accessible platform containing information on certification schemes, technical specifications, certificates, EU statements of conformity and their status, including suspended or withdrawn certificates.
Chart 1 – Scheme development
Chart 2 – Scheme maintenance
Table 2. Workflow for the Development of European Cybersecurity Certification Schemes
| Step | Description | Commission | ENISA | ECCG | Member States | Outputs / Documents | Legal basis |
| 1. Identification of need | Identification of the need for a certification scheme | May decide to initiate | May suggest development of a scheme | May contribute to identifying needs | Initial input / policy need | Article 73 | |
| 2. Request to ENISA | Formal request defining scope and objectives of the scheme | Prepares and adopts request | Receives request | May provide input | May be consulted | Commission request to ENISA | Article 73 |
| 3. Preparation of candidate scheme | Drafting of the certification scheme | Prepares candidate scheme | Participates in discussions | Participate in discussions | Draft / candidate scheme | Article 74 | |
| 4. Stakeholder consultation | Consultation of stakeholders and experts | Organises consultations and may establish ad hoc working groups | Participates / exchanges views | Participate | Consolidated feedback | Articles 74 and 75 | |
| 5. Finalisation of candidate scheme | Integration of feedback and final draft | Finalises candidate scheme | Provides opinions / input | Provide input | Final candidate scheme | Article 74 | |
| 6. Submission to Commission | Transmission of candidate scheme | Receives submission | Submits scheme | Candidate scheme submitted | Article 74 | ||
| 7. Assessment of scheme | Evaluation of the candidate scheme | Assesses scheme; may accept, request revision or discontinue | Supports if needed | May provide views | Assessment outcome | Article 74 | |
| 8. Adoption of scheme | Formal adoption of the scheme | Adopts implementing act | Implementing act establishing the scheme | Article 74 | |||
| 9. Publication and information | Publication of scheme and related information | Publishes scheme and documentation | Published scheme / website entries | Articles 72 and 79 | |||
| 10. Implementation and use | Certification activities under the scheme | Supports implementation and guidance | Facilitates coordination | Apply scheme at national level | Certificates / EU statements of conformity | Articles 71, 85 | |
| 11. Maintenance of scheme | Ongoing updates and adjustments | Participates (consultative role) | Coordinates maintenance activities | Exchanges views / provides input | Contribute to implementation feedback | Updated specifications / scheme updates | Article 75 |
| 12. Evaluation and review | Periodic evaluation and possible revision or withdrawal | Decides to maintain, revise or withdraw (implementing act) | Evaluates schemes | Provides opinions | May contribute | Evaluation report / review outcome | Article 76 |
| 13. Technical specifications | Development of supporting technical specifications | Develops and publishes technical specifications | May exchange views | Technical specifications (some may not be public) | Article 77 |
Chart 3. Interaction of European cybersecurity certification schemes with Union legal frameworks
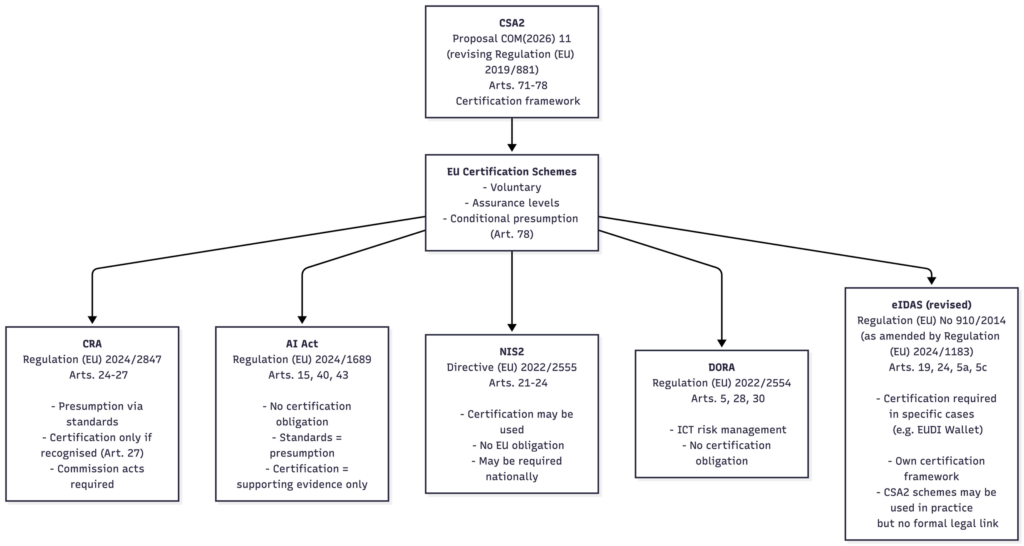
Table 2. Interaction of European Cybersecurity Certification with Union Legal Frameworks
| Instrument | Legal reference | Nature of obligation | Role of certification | Legal effect of certification |
| CSA2 | Proposal COM(2026) 11 (revising Regulation (EU) 2019/881) | Establishes EU certification framework | Creates European cybersecurity certification schemes (voluntary) | May provide presumption of conformity where referenced in Union law (Art. 78) |
| CRA | Regulation (EU) 2024/2847 | Mandatory product cybersecurity requirements | Certification may be used if recognised under Union law | May provide presumption of conformity only if referenced in implementing/delegated acts (Art. 27) |
| AI Act | Regulation (EU) 2024/1689 | Mandatory requirements for high-risk AI systems | Certification may be used as supporting evidence | No presumption of conformity; compliance based on standards and conformity assessment (Arts. 40, 43) |
| NIS2 | Directive (EU) 2022/2555 | Risk-management obligations | Certification may be used to demonstrate compliance | No EU-level obligation; may become mandatory at national level through transposition (Arts. 21, 24) |
| DORA | Regulation (EU) 2022/2554 | ICT risk management for financial sector | Certification may support risk management and third-party assurance | No presumption of conformity; no certification obligation |
| eIDAS (revised) | Regulation (EU) No 910/2014 as amended by Regulation (EU) 2024/1183 | Security and certification requirements for trust services and EUDI Wallet | Certification required in specific cases (e.g. EUDI Wallet) | Operates under its own framework; no formal legal link or presumption via CSA2 |
Chapter II – Content of certification schemes (Articles 80-84)
Article 80 – Security objectives and requirements
Article 80 defines the security objectives of certification schemes, including requirements related to secure design and operation, protection of confidentiality, integrity, availability and authenticity, prevention of unauthorised access, vulnerability identification, monitoring, resilience, coordinated vulnerability disclosure and appropriate governance and risk management.
Article 81 – Mandatory and optional elements of schemes
Article 81 specifies the elements to be included in certification schemes, including scope, purpose, applicable legislation, cybersecurity requirements, evaluation methods, assurance levels, certificate validity, lifecycle management, compliance monitoring and vulnerability handling, as well as optional elements such as labels and peer assessment mechanisms.
Article 82 – Assurance levels and evaluation framework
Article 82 establishes the assurance levels “basic”, “substantial” and “high”, defining corresponding evaluation activities, testing requirements and conditions for conformity assessment and certification.
Article 83 – Conformity self-assessment regime
Article 83 allows for conformity self-assessment at the basic assurance level, enabling economic operators to issue EU statements of conformity under their responsibility, subject to documentation and notification requirements.
Article 84 – Supplementary cybersecurity information obligations
Article 84 requires manufacturers and providers to supply supplementary cybersecurity information, including guidance on secure use, configuration, maintenance and vulnerability handling, while allowing for justified limitations where disclosure may affect security.
CHAPTER III – Governance for the European Cybersecurity Certification Framework
Section 1- General rules and management of European cybersecurity certification schemes
Article 85 – Issuance, validity and post-certification obligations
Article 85 governs the issuance of European cybersecurity certificates and EU statements of conformity for ICT products, services, processes, managed security services and the cybersecurity posture of entities. It defines the roles of conformity assessment bodies and, where applicable, public authorities in issuing certificates, including stricter conditions for certificates at higher assurance levels. The Article establishes requirements concerning the validity period, renewal and suspension or withdrawal of certificates, and sets out obligations for certificate holders, including notification duties to ENISA and national authorities, as well as requirements related to post-certification monitoring, including the reporting and handling of vulnerabilities.
Article 86 – Relationship between European and national certification schemes
Article 86 regulates the coexistence of European and national cybersecurity certification schemes. It provides that national schemes covering the same scope as a European scheme cease to produce legal effects once the European scheme becomes applicable. It prohibits the introduction of new national schemes overlapping with European schemes and establishes transitional provisions ensuring that certificates issued under national schemes remain valid until their expiry. It also provides for notification and coordination mechanisms between Member States, the Commission and the European Cybersecurity Certification Group.
Article 87 – International recognition and equivalence mechanisms
Article 87 establishes the framework for the international recognition of European cybersecurity certificates. It provides that such recognition may be granted through implementing acts adopted by the Commission or through international agreements, subject to reciprocity and compliance with predefined conditions. It sets out the criteria and procedures for assessing equivalence of third-country certification schemes.
Article 88 – Designation, tasks and powers of national certification authorities
Article 88 requires Member States to designate one or more national cybersecurity certification authorities responsible for the supervision and enforcement of certification schemes. It establishes requirements concerning their independence, resources and organisational separation between certification and supervisory functions. The Article defines their tasks, including monitoring compliance, authorising conformity assessment bodies where required, cooperating with ENISA and other authorities, and exercising investigative and corrective powers, such as requesting information, conducting inspections, suspending or withdrawing certificates and imposing penalties.
Article 89 – Peer review mechanism for national certification authorities
Article 89 establishes a peer review mechanism applicable to national cybersecurity certification authorities. It provides that the mechanism shall assess the functioning, performance and compliance of those authorities with the requirements set out in the Regulation and in applicable certification schemes. The Article defines the scope and criteria of peer reviews, including aspects related to supervisory practices, authorisation and monitoring of conformity assessment bodies, and the consistent application of certification schemes across Member States. It provides for the organisation of peer review exercises involving other national authorities, with the support of ENISA and the Commission. The Article further establishes procedures for conducting reviews, including the preparation of reports, the identification of findings and possible recommendations. It also provides for the adoption and publication of summaries of peer review outcomes, while ensuring appropriate handling of confidential information.
Article 90 – European Cybersecurity Certification Group (ECCG)
Article 90 establishes the European Cybersecurity Certification Group, defining its composition as representatives of Member States and the Commission, with ENISA providing support. It sets out the tasks of the ECCG, including advising the Commission on certification policy, contributing to the development, maintenance and evaluation of certification schemes, facilitating cooperation and information exchange between national authorities, and supporting international cooperation. It also provides for the establishment of sub-groups and the organisation of its working methods.
Section 2 – Conformity assessment bodies
Article 91 – Accreditation of conformity assessment bodies
Article 91 establishes the framework for the accreditation of conformity assessment bodies by national accreditation bodies in accordance with Union law. It defines the requirements for competence, independence and impartiality, provides for the duration and renewal of accreditation, and requires the suspension or withdrawal of accreditation where conditions are no longer met. It also encourages consistency and cooperation between accreditation bodies across Member States.
Article 92 – Authorisation of conformity assessment bodies
Article 92 introduces additional authorisation requirements for conformity assessment bodies where certification schemes include specific conditions. It sets out procedures for granting, maintaining, restricting or withdrawing such authorisations by national cybersecurity certification authorities, including coordination between Member States and alignment with accreditation processes. It also provides for the adoption of implementing acts by the Commission to further specify these procedures where necessary.
Article 93 – Notification of conformity assessment bodies
Article 93 establishes the procedures for notifying accredited and authorised conformity assessment bodies to the Commission and other Member States. It provides for the use of a common electronic notification system and sets out the information to be provided, ensuring transparency and mutual awareness of notified bodies across the Union.
Article 94 – Assessment and challenge of notified bodies
Article 94 provides for a Union-level mechanism allowing the Commission to assess and challenge the competence of notified conformity assessment bodies. It enables the Commission to request information from national authorities, conduct assessments, ensure confidentiality of information and require corrective measures, including the withdrawal of notification where necessary. It also requires Member States to provide for appropriate appeal procedures.
Article 95 – Information obligations and record keeping
Article 95 sets out obligations for conformity assessment bodies to share information with national authorities and ENISA, including notification of certification decisions, changes in status and relevant findings. It also requires the retention of records related to certification activities for a defined period, ensuring traceability and accountability.
Section 3 – Other provisions
Article 96 – Complaints, dispute resolution and remedies
Article 96 establishes the right for natural and legal persons to lodge complaints regarding certification activities or certificates. It defines procedures for handling such complaints, including obligations on authorities to provide information on progress and decisions, and ensures access to judicial remedies in accordance with Union and national law.
Article 97 – Penalties for infringements of the certification framework
Article 97 requires Member States to establish rules on penalties applicable to infringements of the certification framework and certification schemes. It provides that such penalties must be effective, proportionate and dissuasive, and requires Member States to notify the Commission of those rules and any subsequent amendments.
TITLE IV – SECURITY OF ICT SUPPLY CHAINS (Articles 98-117)
Chapter I – Trusted ICT supply chain framework (Articles 98-109)
Article 98 – Scope and objectives of the supply chain framework
Article 98 defines the scope of the trusted ICT supply chain framework by establishing a Union-level mechanism addressing non-technical cybersecurity risks affecting sectors of high criticality and other critical sectors within the meaning of Directive (EU) 2022/2555. It provides for the identification of key ICT assets and the application of proportionate mitigation measures, while clarifying that the framework operates without prejudice to existing obligations under Union and national law and allows Member States to maintain or adopt higher standards compatible with Union law.
Article 99 – Union-level coordinated risk assessments
Article 99 establishes procedures for coordinated risk assessments at Union level, including the possibility for the Commission or Member States to request such assessments through the NIS Cooperation Group. It specifies the required content, timelines and outcomes of the assessments, including the identification of risks related to ICT supply chains, and provides for expedited procedures led by the Commission where significant threats to the internal market are identified.
Article 100 – Designation of high-risk third countries
Article 100 provides for the designation of third countries presenting serious and structural non-technical cybersecurity risks. It sets out the criteria and verification procedures for such designation and provides that the Commission adopts implementing acts to formalise the designation. It also establishes the consequences for suppliers linked to those countries, including restrictions related to participation in certification schemes, standardisation processes, procurement and access to Union funding, as well as the withdrawal of existing certifications where applicable.
Article 101 – Activation of Union supply chain security measures
Article 101 enables the Commission, following the completion of relevant risk assessments, to activate Union-level ICT supply chain security measures through implementing acts. It provides the legal basis for adopting further measures necessary to address identified risks, including those affecting the functioning of the internal market.
Article 102 – Identification of key ICT assets
Article 102 establishes the framework for identifying key ICT assets subject to supply chain security measures. It sets out the criteria to be taken into account, including the criticality of the asset, the degree of dependency on specific suppliers, the vulnerability of the asset and its potential impact on the internal market, and provides for the adoption of implementing acts specifying such assets.
Article 103 – Mitigation measures and requirements
Article 103 establishes a comprehensive set of mitigation measures that may be applied to address identified risks. These include technical, organisational and contractual measures, requirements related to supply diversification, and restrictions or prohibitions on the use of ICT components from high-risk suppliers. The Article also provides for proportionality, consultation of stakeholders, periodic review of measures and the possibility of emergency procedures where necessary.
Article 104 – Identification and listing of high-risk suppliers
Article 104 provides for the identification and listing of high-risk suppliers. It sets out the procedures for mapping and assessing suppliers, including criteria relating to establishment, ownership and control, and provides for information-gathering powers, cooperation with competent authorities and regular updates of the list through implementing acts.
Article 105 – Exemption mechanism
Article 105 establishes a mechanism for granting exemptions to entities affected by supply chain security measures. It defines the substantive and procedural conditions for exemptions, including assessment criteria, timelines for decisions, possible limitations and monitoring obligations, as well as the grounds and procedures for withdrawal of exemptions.
Article 106 – Rights of defence
Article 106 ensures that entities concerned by decisions adopted under the supply chain framework are granted rights of defence. It provides for the right to be heard prior to the adoption of adverse decisions and establishes procedural safeguards to ensure fairness in decision-making processes.
Article 107 – Public register of exemptions
Article 107 provides for the establishment and maintenance by the Commission of a public register of exemption decisions. It requires that the register be regularly updated and made accessible, ensuring transparency regarding granted exemptions.
Article 108 – Use and protection of information
Article 108 governs the use of information obtained in the context of procedures under Articles 104 to 106. It establishes limitations on the use of such information and provides for confidentiality requirements to ensure that information is used solely for its intended purposes.
Article 109 – Fees for exemption procedures
Article 109 establishes the framework governing fees applicable to requests for exemptions submitted under the ICT supply chain security framework. It provides that fees shall be levied in connection with the assessment of exemption requests and shall be calculated on a cost-recovery basis, ensuring that the resources required for processing applications, including administrative, technical and procedural activities, are covered. The Article specifies that fees are payable in euro and may vary depending on the nature, complexity and scope of the exemption request. It further provides that the Commission shall adopt implementing acts to determine the level of fees, the modalities for their payment, and the detailed procedures applicable to their collection. The Article also establishes that the payment of fees is a condition for the processing of exemption requests, and that the framework shall ensure transparency and proportionality in the calculation and application of fees.
Chart 4. Decision-making process under the ICT supply chain security framework (Articles 98–109)
Table 4. Functioning and Responsibilities under Title IV – Security of ICT Supply Chains (Articles 98–109)
| Article | Mechanism / Area | Main actors | Functioning and responsibilities |
| Article 98 | Scope and framework | Commission, Member States | Establishes a Union framework addressing non-technical cybersecurity risks in ICT supply chains, including the identification of key ICT assets and the application of mitigation measures, while preserving existing Union and national obligations. |
| Article 99 | Coordinated risk assessments | Commission, Member States, NIS Cooperation Group | Provides procedures for Union-level coordinated risk assessments, including requests by the Commission or Member States, definition of scope, timelines and outcomes, and the possibility of expedited assessments led by the Commission. |
| Article 100 | Designation of high-risk third countries | Commission | Establishes criteria and procedures for designating third countries presenting serious cybersecurity risks through implementing acts, including the consequences for suppliers linked to such countries. |
| Article 101 | Activation of Union measures | Commission | Empowers the Commission to activate ICT supply chain security measures following relevant risk assessments, through implementing acts. |
| Article 102 | Identification of key ICT assets | Commission | Provides for the identification of key ICT assets subject to security measures, based on criteria such as criticality, dependency, vulnerability and impact, through implementing acts. |
| Article 103 | Mitigation measures | Commission, Member States, stakeholders | Establishes a set of mitigation measures, including technical, organisational and contractual requirements, as well as restrictions or prohibitions, with provisions on proportionality, consultation and periodic review. |
| Article 104 | Identification of high-risk suppliers | Commission, competent authorities | Sets procedures for identifying and listing high-risk suppliers, including mapping, assessment of establishment, ownership and control, information gathering and regular updates. |
| Article 105 | Exemption mechanism | Commission, concerned entities | Establishes procedures for granting exemptions, including conditions, assessment criteria, timelines, monitoring obligations and grounds for withdrawal. |
| Article 106 | Rights of defence | Commission, concerned entities | Provides procedural safeguards ensuring that entities concerned are heard before the adoption of adverse decisions. |
| Article 107 | Public register of exemptions | Commission | Requires the establishment and maintenance of a public register of exemption decisions, ensuring transparency. |
| Article 108 | Use of information | Commission, authorities | Establishes rules on the use and protection of information obtained in procedures, including confidentiality requirements and purpose limitation. |
| Article 109 | Fees for exemption procedures | Commission, applicants | Provides for cost-based fees applicable to exemption requests and for the adoption of implementing acts specifying fee levels and payment modalities. |
Chapter II – ICT supply chains in electronic communications networks (Articles 110-111)
Article 110 – Key ICT assets and phase-out obligations in electronic communications networks
Article 110 identifies key ICT assets within mobile, fixed and satellite electronic communications networks and establishes obligations for phasing out ICT components from high-risk suppliers. It sets a maximum period for the phase-out of such components in mobile networks and empowers the Commission to determine corresponding timelines for fixed and satellite networks through implementing acts. It also provides for the amendment of the list of key ICT assets through delegated acts to reflect technological developments.
Article 111 – Prohibition of high-risk suppliers in key ICT assets
Article 111 establishes a prohibition on the use, installation or integration of ICT components from high-risk suppliers in key ICT assets within electronic communications networks. It further requires coordination and information exchange between competent authorities where supervisory responsibilities are shared, ensuring consistent application and enforcement.
Chapter III – Competent authorities, supervision and enforcement (Articles 112-117)
Article 112 – Designation of competent authorities
Article 112 requires Member States to designate competent authorities responsible for supervising and enforcing the supply chain framework, aligning those responsibilities with the authorities designated under Directive (EU) 2022/2555.
Article 113 – Cooperation network and coordination mechanisms
Article 113 establishes a cooperation network between national competent authorities and the Commission. It provides a structured framework for information exchange, coordination of supervisory activities and support for assessments related to establishment, ownership and control, with administrative support ensured by the Commission.
Article 114 – Supervisory and enforcement powers
Article 114 defines the supervisory and enforcement powers of competent authorities, including the ability to request information, carry out inspections and audits, issue warnings, adopt binding decisions, require corrective measures and impose penalties. It also establishes requirements regarding proportionality, procedural safeguards, confidentiality and coordination with other authorities and the Commission.
Article 115 – Penalties and sanctioning regimes
Article 115 requires Member States to establish effective, proportionate and dissuasive penalty regimes for infringements of the supply chain framework. It specifies criteria for determining penalties, including the nature and gravity of the infringement, and provides for maximum levels linked to worldwide annual turnover.
Article 116 – Mutual assistance and cross-border cooperation
Article 116 provides for mutual assistance between competent authorities and the Commission in cross-border situations. It establishes obligations to exchange information, cooperate in investigations, provide assistance on a best-efforts basis and conduct joint supervisory actions where appropriate, subject to confidentiality and proportionality safeguards.
Article 117 – Jurisdiction and territorial application
Article 117 establishes rules on jurisdiction and territorial application of the supply chain framework. It provides criteria for determining the competent authority based on establishment or service provision, requires entities established outside the Union to designate a representative within the Union, and allows Member States to take enforcement action within their territory in coordination with other authorities.
TITLE V – FINAL PROVISIONS (Articles 118-122)
Chapter I – Committee procedure and delegated powers (Articles 118-119)
Article 118 – Committee procedure and comitology arrangements
Article 118 establishes that the Commission is assisted by a committee within the meaning of Regulation (EU) No 182/2011. It provides that the committee operates in different configurations corresponding to the certification framework and the ICT supply chain security provisions. The Article specifies that the examination procedure applies where implementing acts are adopted, and clarifies the procedural framework governing the involvement of Member States in the adoption of such acts.
Article 119 – Exercise of delegated powers by the Commission
Article 119 sets out the conditions under which the Commission may exercise delegated powers under the Regulation. It provides that the Commission shall consult experts designated by Member States prior to the adoption of delegated acts, establishes the procedures for notification of such acts to the European Parliament and the Council, and defines the conditions under which delegated acts may enter into force or be objected to or revoked by the co-legislators.
Chapter II – Evaluation, repeal and entry into force (Articles 120-122)
Article 120 – Evaluation and review of the Regulation
Article 120 requires the Commission to carry out an evaluation of the Regulation by a specified date and subsequently at regular intervals of five years. It defines the scope of the evaluation, including the assessment of ENISA’s performance, mandate and governance, the effectiveness of the European cybersecurity certification framework, the functioning of cybersecurity skills attestation schemes, and the implementation of the ICT supply chain security framework. It further requires the Commission to report its findings to the European Parliament, the Council and the Management Board of ENISA, and to make the evaluation publicly available.
Article 121 – Repeal and transitional provisions
Article 121 repeals Regulation (EU) 2019/881 and establishes transitional provisions to ensure continuity of ENISA’s activities and legal framework. It provides that existing agreements, administrative arrangements, decisions, financial commitments, employment contracts and certification schemes adopted under the previous Regulation remain valid. It also ensures continuity in the composition and functioning of ENISA’s governing bodies and maintains the validity of ongoing procedures and candidate certification schemes.
Article 122 – Entry into force and application
Article 122 provides that the Regulation shall enter into force on the twentieth day following its publication in the Official Journal of the European Union. It establishes that the Regulation is binding in its entirety and directly applicable in all Member States in accordance with the Treaties.